-
Positions
-

Part time technical support
Position: Technical supportNumber of places: 12Applicants: 16 -
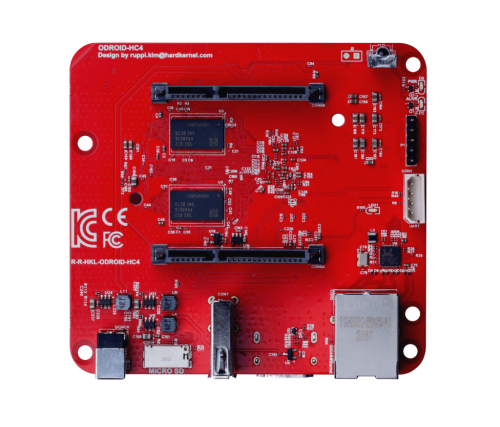
Single board computer maintainer
Position: Board maintainerNumber of places: 64Applicants: 76 -

Code reviewer
Position: Framework maintainerNumber of places: UnlimitedApplicants: 11 -

Test Automation Engineer
Position: Software integration test engineerNumber of places: 16Applicants: 10 -

Build framework maintainer
Position: Framework maintainerNumber of places: 16Applicants: 6
-
-
Chat | Social Media
#armbian at
irc.libera.chat or irc.oftc.net
Matrix or Discord
Mastodon | 𝕏 -
Popular Now
-
Activity Stream
-
3
current kernel from apt repo (6.16.8-edge-sunxi64) still vulnerable to local privilege escalation bug CVE-2026-31431 "copy.fail"
This, even though serious, it's "only" a privilege escalation, not remote code execution (RCE), so if someone were to use this on you, they would first need to have physical access OR access remotely (RCE) to be able to run the exploit and escalate to root. And if you have a malware with RCE, you are already f**ed. In time, I'm pretty sure upstream patches will spread down to armbian builds too. For explanation see for example https://www.reddit.com/r/linux/comments/1t29iwr/why_isnt_copyfail_patched_on_some_distro_versions/ In the meantime if you think someone might be able to get access and escalate, you can disable algif_aead (or try to apply patches yourself) as mentioned in https://xint.io/blog/copy-fail-linux-distributions -
3
Fsck system fs read-only, but don't boot
He meant this forum-post was moved to "staging". Maybe someone in the community will be able to help. (I can't help much with your problem, only explain what he meant with the post) Try what yourself suggested, run fsck from another system and see. But if a filesystem becomes readonly, it can mean that the drive is starting to fail physically. -
3
current kernel from apt repo (6.16.8-edge-sunxi64) still vulnerable to local privilege escalation bug CVE-2026-31431 "copy.fail"
I understand that you're overworked and underpaid. This is free software, so I won't demand more labor from any of you. That said, I think it would build trust to at least have a little temporary pop-up (not the right word but I dont know what it's called) on the homepage that says something like "Current kernels may be vulnerable to this bug, we're working to resolve this, here are some relevant links" and then post the kernel dot org patch for this bug and point people to the Armbian build system. Surely the amount of effort it would take to do that is equal to or even less than it took to give me such a thorough response (which I appreciate btw). -
30
ESPRESSObin Firmware/Bootloader
Thanks @bschnei! It built successfully. -- Success: NTIM Processing has completed successfully! Finish time: 05/05/26 20:14:07 TBB Exiting...! No input file for TIMN is supplied Total number of images to process in file[0] - 3 0 Image at offset 00000000 is TIM_ATF.bin 1 Image at offset 00004000 is wtmi.bin 2 Image at offset 00015000 is boot-image.bin Total number of images 3 Built ebu-bootloader/trusted-firmware-a/build/a3700/release/flash-image.bin successfully -
179
Gaming experience with Orange Pi 5 (RK3588) on Armbian
I have been using Proton 11 Arm64 for weeks. It has good compatibilities in general (some games I have tested still broke). However, I prefer Proton 11 (Box64), it gives better performance.
-
-
Member Statistics


