-
Posts
510 -
Joined
-
Last visited
Content Type
Forums
Store
Crowdfunding
Applications
Events
Raffles
Community Map
Everything posted by Nick A
-
@Gavin Munday Did you compile a desktop or server image? Did you write the image onto a reliable sdcard? Remember there’s no framebuffer support. Server images need a usb to serial device attached to the UART. Having a usb serial device attached to the UART helps with these types of problems. https://docs.radxa.com/en/cubie/a7a/system-config/uart_debug Also, first boot might take awhile to boot. For desktop images wait at least 5 minutes for a display manager login screen.
-
@Gavin Mundayhttps://github.com/NickAlilovic/build/blob/Radxa-A7A/config/boards/radxa-cubie-a7z.csc
-
@zmxyz I added support for A7Z. But I haven't tested it yet. I don't own a A7Z. Compile an image and let me know if it works.
-
@Jeeva Kandasamy depends on which branch you are looking at? V20250306 hasn’t changed much. https://github.com/NickAlilovic/build/commits/v20250306/
-
@dale I had the same problem last night. Should be fixed now. Clone or update the repository. You will need to install Docker. https://github.com/NickAlilovic/build/commit/025e4487f87233bfb823c7d51162d877b2a9fd6f https://github.com/armbian/build/issues/8572
-
@Jeeva Kandasamy I noticed the same problem with my older builds. Should be fixed now. You'll need to install Docker. Also, if you see the build-root errors. Run the same compile options again and it continue where you left off.
-
Thanks @dale I'll test it out on my box first and add it later on today.
-
I found this thread https://forum.armbian.com/topic/47929-banana-pi-bpi-m2-ultra-with-armbian-stops-load-after-scanning-for-btrfs-filesystems/
-
@Shubham Singh To check if KVM is compiled into the kernel, use the following command: grep CONFIG_KVM /boot/config-$(uname -r) CONFIG_KVM=y CONFIG_KVM_MMIO=y CONFIG_KVM_VFIO=y CONFIG_KVM_GENERIC_DIRTYLOG_READ_PROTECT=y CONFIG_KVM_XFER_TO_GUEST_WORK=y A7A: Harware Virtualization https://forum.radxa.com/t/a7a-harware-virtualization/29745
-
@djoness you need to Disable Armbian kernel/firmware upgrades using the armbian-config tool. System -> Updates -> UPD002 - Disable Armbian firmware upgrades -> Disable Armbian kernel/firmware upgrades X96Q has many different variations of the same box. Read the bottom of this thread. https://github.com/warpme/miniarch/issues/102 If you want a well supported box get a Transpeed 8K618-t.
-

"This DRAM setup is currently not supported."
Nick A replied to qwerty keyboard's topic in Allwinner CPU Boxes
An apt error related to ntpdate typically indicates a time synchronization issue, as apt relies on accurate system time for validating package release files. https://www.google.com/search?sca_esv=55588fd05011d482&rlz=1CDGOYI_enCA922CA922&hl=en-US&sxsrf=AE3TifMjcn14YNfEQNUHV48vtdb2hNOADw:1763573317647&q=How+to+fix+apt+error+around+ntpdate&sa=X&ved=2ahUKEwiLzojJ3v6QAxUbEFkFHatLG24Q1QJ6BAgQEAE&biw=390&bih=665&dpr=3 -

"This DRAM setup is currently not supported."
Nick A replied to qwerty keyboard's topic in Allwinner CPU Boxes
@qwerty keyboard H313/H616/H618 are pretty much the same. A133 and A64 are different SOC’s. You don’t need the dts for the dram settings. -
@djonessIf you can find the source code for this image that would help. MiniArch-20231112-6.6.2-board-h313.x96_q-SD-Image.img Have you tried miniarch latest images?
-
@djoness My build uses the miniarch patches. https://github.com/NickAlilovic/build/releases/tag/20250306 Here's a direct link to X96q ddr3 server image. https://github.com/NickAlilovic/build/releases/download/20250306/Armbian-unofficial_25.05.0-trunk_X96q-ddr3_bookworm_edge_6.12.11_server.img.xz
-

"This DRAM setup is currently not supported."
Nick A replied to qwerty keyboard's topic in Allwinner CPU Boxes
@qwerty keyboard here are some links that will help you. Find your Dram settings https://forum.armbian.com/topic/29794-how-to-install-armbian-in-h618/#findComment-218660 Find boot.bin and extract dts. https://forum.armbian.com/topic/29794-how-to-install-armbian-in-h618/#findComment-187672 Uboot defconfig. I have two x96q builds with ddr3. https://github.com/NickAlilovic/build/blob/v20250306/patch/u-boot/u-boot-h616/151-add-x96-q-ddr3-defconfig.patch Or https://github.com/NickAlilovic/build/blob/v20250306/patch/u-boot/u-boot-h616/163-add-x96-q-ddr3-v5.1-defconfig.patch You can edit the patch and enter the new values. If you need to add a new line in the defconfig patch. At the bottom of the patch add your newline and put a "+" infront of it. Also, for x96q ddr3 increase @@ -0,0 +1,37 @@ to @@ -0,0 +1,38 @@ or for x96q ddr3 v5.1 @@ -0,0 +1,39 @@ to @@ -0,0 +1,40 @@. Download and compile my build: git clone https://github.com/NickAlilovic/build.git --branch v20250306 cd build ./compile.sh choose "Do not change kernel configuration" choose "Show CSC/WIP/EOS/TVB" choose "I understand and agree" choose "X96Q DDR3” or “X96Q DDR3 v5.1” choose "edge" rest is up to you. -
@blackc Exact the original U-boot DRAM settings from your boot.bin or an update. https://forum.armbian.com/topic/29794-how-to-install-armbian-in-h618/page/23/#findComment-218660 If you are still having issues ask the sunxi guys on IRC. https://oftc.catirclogs.org/linux-sunxi/2025-11-14
-
Fixed the automatic first boot configuration on Bookwarm. Now you can boot the desktop image without a usb serial device.
-
You need to set this to y or m in your kernel config. https://github.com/NickAlilovic/build/blob/v20250306/config/kernel/linux-sunxi64-edge.config#L5745 https://www.kernelconfig.io/config_usb_acm
-
@eli It's compiled in the kernel https://github.com/NickAlilovic/build/blob/Radxa-A7A/config/kernel/linux-sun60i-legacy.config#L1659-L1672
-
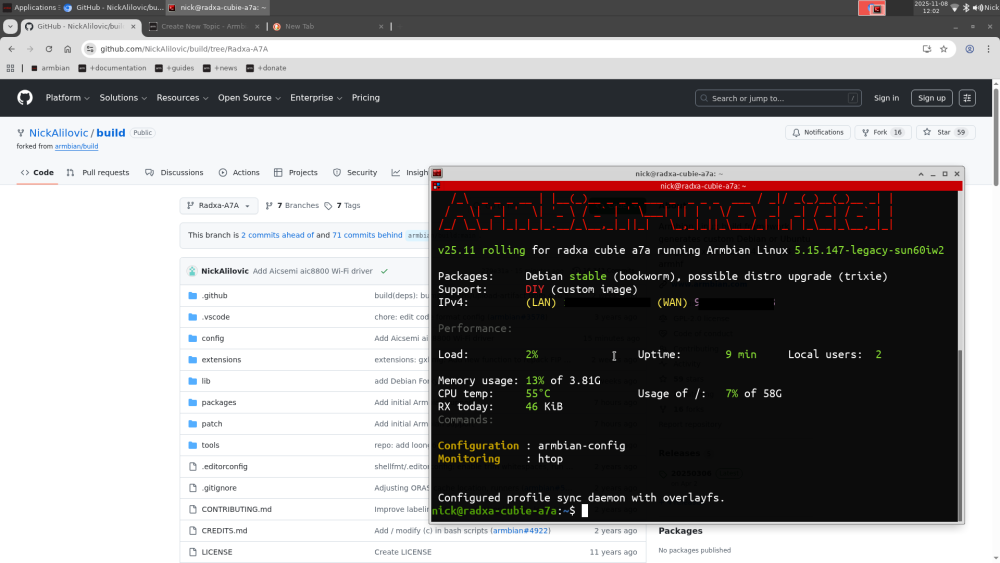
For those with a Radxa Cubie A7A/A7Z, I made a custom Armbian Build using the BSP kernel. https://github.com/NickAlilovic/build/tree/Radxa-A7A https://github.com/NickAlilovic/build/releases/tag/Radxa-a7a-v0.4 To build your own image: git clone https://github.com/NickAlilovic/build.git --branch Radxa-A7A ./compile.sh "do not change the kernel configuration" "show csc/wip/eos/tvb" "I understand and agree" "radxa-cubie-a7a" or "radxa-cubie-a7z" rest is up to you... - Display: Installed KMSCON framebuffer console (KMS/DRM-based system console) to provide a modern system console. - Boot: Added sfdisk labeling for the 'primary' partition to ensure U-Boot splash screen and logo.bmp detection. - U-Boot: Automated latest-release retrieval from GitHub API (radxa-pkg/u-boot-aw2501) to replace static binaries. - Kernel Device: Automated copying of allwinner device a733 and added 0004-Add-Allwinner-Device-a733.patch generation for a7a, a7s, and a7z device tree variants.
-
@emor acid The build system downloads the original uboot and kernel sources. Then it applies the patches on top. Whatever you edited will be erased. The only way around this is to create a patch with your changes. You could use dtc to compile your dts file into a binary dtb. Then copy it into your sdcard.
-

Cannot run ARMbian on my tv box (TX10 PRO)
Nick A replied to erebus041's topic in Allwinner CPU Boxes
@Farhan Ishraq Have you tried the images in the link @Sadiq Ahmed posted? Download BalenaEtcher software. Write one of the bigtreetech cb1 images onto a SDcard. Put it in your box and boot. -

TX95 Max - Allwinner H618 Quadcore Cortex - A53
Nick A replied to Mark Waples's topic in Allwinner CPU Boxes
@Gilliard Gabriel Rodrigues Mark was using my Transpeed image. https://github.com/NickAlilovic/build/releases/tag/20250306 -
@ayoub-hs I don't own one of these boxes. I got the patches from warpme's miniarch/minimyth2. Supporting the x96q is a real PITA. https://github.com/warpme/miniarch/issues/102 Comparing the uboot DTS for both x96q lpddr3 and x96q lpddr3 v1.3. I don't see much difference other than wifi. Maybe you'll find something I missed. u-boot: https://github.com/NickAlilovic/build/blob/v20250306/patch/u-boot/u-boot-h616/159-add-x96-q-lpddr3-v1.3-defconfig.patch https://github.com/NickAlilovic/build/blob/v20250306/patch/u-boot/u-boot-h616/150-add-x96-q-lpddr3-defconfig.patch Kernel: https://github.com/NickAlilovic/build/blob/v20250306/patch/kernel/archive/warpme-6.12/0648-arm64-dts-allwinner-h313-add-x96q-lpddr3-TVbox.patch https://github.com/warpme/minimyth2/tree/master/script/bootloaders https://github.com/warpme/minimyth2/tree/master/script/bootloaders/u-boot-aw/files
-
@leXia "no matter which image I use, it always boots into Android". Maybe it's not booting into FEL mode or it's not reading your SDcard. To enter FEL mode, power off the TV box, insert your SDcard, press and hold a hidden button (often inside the AV port, reachable with a toothpick) while connecting the power cable, release the button after a few seconds. If that doesn't work try another SDcard. Usually, if you box detects uboot and stops you'll just get a black screen. Without UART communication I can't really help. If it boots the kernel then you can check your SDcard for log files.